What is SPF Record: How to Create, Optimize and Check It

This article will teach you what an SPF record is and how you can create an SPF TXT record that’s optimized to pass SPF authentication, protect you from spam, and improve your email deliverability.
Who can benefit from this article?
- Email service providers who send email on behalf of their clients and need their clients to include an SPF record in their domain’s DNS (Domain Names System)
- Email senders who are learning how to publish their own SPF records within their domain’s DNS.
We will cover:
What is SPF Record?
An SPF record is a form of authentication that prevents spammers from spoofing your domain and ruining your reputation. It allows you to choose what IP addresses are authorized to send email on behalf of your domain by publishing a TXT record in your DNS records.
SPF stands for Sender Policy Framework. It proves to ISP mail servers like Gmail, Yahoo!Mail, or Microsoft Exchange/ Outlook that incoming messages came from an authorized source. However, SPF alone will not fully protect your domain from spoofing. It is always recommended that you set up Sender Policy Framework along with DKIM, BIMI, and DMARC protocols.
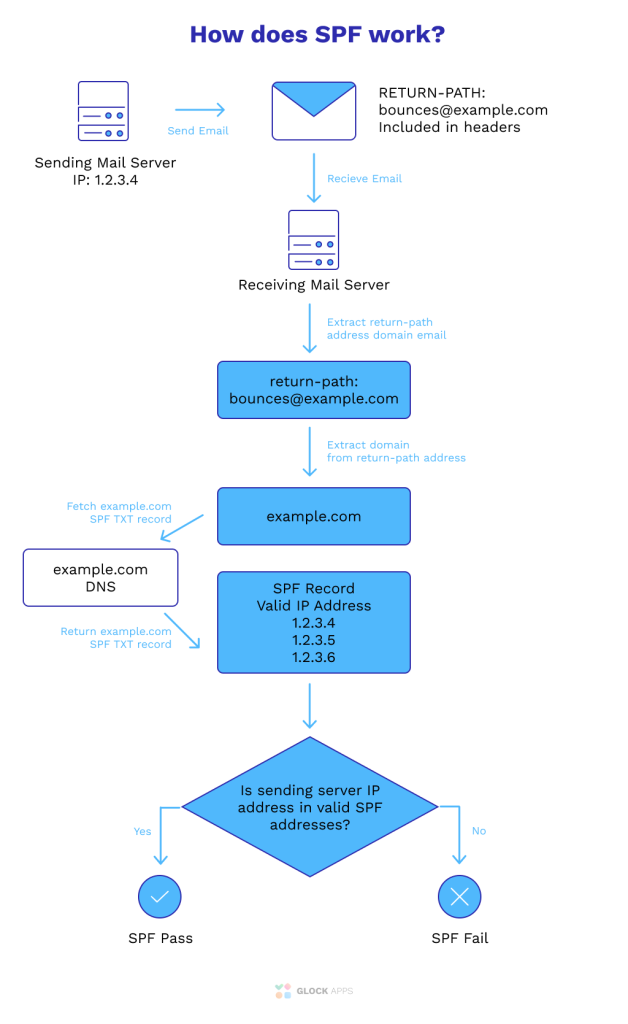
How SPF Records Work
Your SPF record lists which IPs are authorized to send messages from your domain. When the email reaches your recipient’s mail server, the mail server looks at your IP by pulling it from the “Envelope From” address. If the message was spoofed, the IP will be different from the mail servers authorized in the DNS record. In this case, the email will be rejected by the receiving mail server.
How to Create SPF Record
To create an SPF record you have to define which IPs or senders are authorized to send emails on your behalf. Follow these steps to generate a new SPF record:
- Start with this tag: v=spf1 – it indicates the SPF version and always stays v=spf1.
- Follow this tag with IPs or sending domains that are allowed to send emails from you (example: v=spf1 ip4)
- If you send emails from a third-party organization, don’t forget to add it as an authorized sender. To do so add include:thirdpartydomain.com.
- End the record with -all (fail/hardfail) – it indicates that all IPs that don’t match with the ones you have provided will be rejected by your recipients’ email servers. Another modifier for this option is ~all (softfail); it means that emails from any unauthorized IPs will be accepted by the receiving mail server, but marked as spam.
- Once your record is ready, go to your hosting provider to publish it. Now, any receiving mail server will know if a sender is authorized to send email on behalf of your domain.
Learn More Information about SPF Soft Fail – Everything about SPF Failures
SPF Record Syntax You Need to Know:
- ip4 – indicates the IP address of a sender in Internet Protocol version 4 (IPv4) or the specified IPv4 subnet that contains it
- ip6 – indicates the IP address of a sender in Internet Protocol version 6 (IPv6) or the specified IPv4 subnet that contains it
- mx – specifies that if the domain name has a mail exchanger (MX) record, it should match the domain of a sending source
- a – if a sender has an address record (A or AAAA), it should resolve to the sender’s address
SPF Record Example
Once you’ve finished setting up your SPF TXT record, it should look something like this example record:
v=spf1ip4:30.1124.300.302 include:thirdpartydomain.com ~all
The SPF TXT record above starts with the version, followed by the authorized IP address(es), then the third party domain is included (if you have one), and finished with a tag -all.
Another example of the way your TXT records can look:
v=spf1 a mx ip4:30.1124.300.302 include:thirdpartydomain.com ~all
Here, the specific domain uses an ‘a’ mechanism and a ‘MX’ mechanism, therefore they are included in the TXT record.
How to Optimize SPF Record Syntax
Maximum SPF Record Limit
The SPF standard methods require that every record must not exceed the 10-lookup limit. SPF record limits state that any record that causes more than 10 DNS queries is not valid. Therefore, if you attempt to authenticate SPF for that specific domain, it will lead to an error.
The “include”, “a”, “MX”, “PTR”, “exists” mechanisms, and the redirect modifier does count against this SPF record limit.
The “all”, “ip4”, and “ip6” mechanisms do not require DNS lookups and therefore, do not count against the SPF 10-lookup maximum limit.
So, how can you optimize your record in order to comply with SPF record limits and be able to contact your customers?
Bypassing SPF Record Limits
Try skipping the “MX” mechanism. It makes a record look simpler, but it always triggers a DNS lookup that counts against the SPF 10-lookup limit.
Instead of “MX”, consider the “ip4” and “ip6” mechanisms to list the IP addresses your host and MX record send emails from. Though your record will look longer, it will be actually smaller from the DNS queries’ perspective. A single “MX” mechanism counts as more than 20 “ip4” mechanisms!
Similarly, avoid the “a” mechanism as it can also be replaced with “ip4” or “ip6”.
Also, don’t use “PTR” as they are frowned upon by the current SPF RFC.
IP Addresses Verification
Make sure you don’t have too many “ip4” and “ip6” mechanisms.
Are there any IP addresses that you are not using? Are there any IP address ranges that can be merged?
For example, “ip4:x.y.z.4/24” and “ip4:x.y.z.5/24” can be replaced with “ip4:x.y.z.4/23”.
CIDR blocks generated from IP address ranges can sometimes give very inefficient representations. The IP range 10.11.12.1-10.11.12.254 needs 14 “ip4” mechanisms to represent precisely. Instead, you can use the single mechanism “ip4:10.11.12.0/24”, even if you’re not sending any email from the .0 or .254 addresses.
You don’t need a “~all” or “-all” at the end of a TXT record that is only included in another record, not used directly. It won’t do any harm but it eats a few characters.
Split Your SPF Record
An SPF record can contain one or more strings of text, but each string cannot contain more than 255 characters. An SPF checker will take all of the strings in a TXT record and bind them together before it starts looking at the content. Thus, you can have more than 255 characters in your record if you split it into more than one string.
But keep your DNS packets less than 512 bytes long. Count the DNS overhead for a single TXT record with two strings (about 34 bytes), then add the length of the hostname that’s being queried. In order to comply with the 512-byte limit, you need to split your SPF into pieces of no more than 478 bytes minus the length of the hostname.
Then you need to split that SPF data into two strings. They will be bonded without any spaces added, so you need to add a space at the end of the first string or the beginning of the second string.
Learn more:
The Ultimate Guide to Email Authentication
How to Manage and Merge Multiple SPF Records
What’s the difference between DKIM AUTH/EVAL and SPF AUTH/EVAL?
Why did I receive an alert about SPF failures?
Test Your SPF Record
GlockApps created an SPF checking tool to help you perform an SPF check and optimize your record.
Enter your domain and click “Check SPF” to check your SPF record. Or you can copy-paste your record to check its syntax.

The GlockApps SPF Record Checker:
- Verifies the SPF record
- Performs an SPF record syntax check
- Makes sure there are less than 10 mechanisms and modifiers that do DNS lookups
FREE SPF RECORD VALIDATOR
SPF Record Syntax Check
With GlockApps DMARC Analyzer, you can identify any unauthorized domains sending email on behalf of your domain. You can also ensure that all your authorized domains pass the SPF, DKIM, and DMARC authentication.
Start using our DMARC Analyzer to get 10,000 free DMARC messages every month for unlimited domains to monitor your email traffic.
Conclusion
Every marketer sending email should know how important it is to not only implement SPF records but also optimize them to protect their sending reputation and avoid email spoofing and phishing attacks.
Only authorized senders will be able to send mail on your behalf without being rejected by mail servers. Be sure to define all sending domains including your primary domain and third-party services in your SPF within your DNS records and exclude any non-sending domain.
In order to achieve the best results from your email marketing efforts and avoid being marked as spam, publish an optimized SPF record and perform an SPF check frequently. This will help ensure any unauthorized mail server is not sending spam mail using your domain.
More Information About SPF:
How to Deploy SPF Email Authentication
12 Questions You Should Be Asking If You Have Deliverability Issues
DMARC: How to Prevent Email Spoofing
DMARC Fail: What Causes DMARC Failure?
How the New Email Uptime Monitoring Helps with Multiple SPF Records
Improving Email Deliverability Using MX, SPF, and PTR Records
Can you tell me why SPF is showing Permerror?
How to avoid SPF failures if the DNS lookup limit is exceeded?
How to Set up SPF Uptime Monitor?
GlockApps Spam Testing for Marketers and Agencies

Test your email placement
Scan your emails through all the major spam filters before you send them.
Improve your deliverability
Get actionable tips for improving the delivery rate of every email you send.
Increase your revenue
Improve your overall email performance by delivering more emails to the inbox.