[Case Study] How DMARC Analytics Helps Save Domain Reputation
Like all companies doing business online and communicating with their clients via email, we, at GSoft, are concerned about our domain reputation. To protect the domain and ensure that nobody is sending spam or phishing emails on behalf of our company, we implemented DMARC email authentication with the ‘reject’ policy.
We thought it was enough to be protected and we were not monitoring our DMARC data in GlockApps DMARC Analytics regularly. But thanks to the GlockApps alert system, we realized that we were wrong.
Below I share our case on how GlockApps alerts helped us find and fix a critical issue with our domain.
To give you some background, here at GSoft, we have a few mailboxes set up on the same domain: support@ourdomain.com, abuse@ourdomain.com, info@ourdomain.com, bounce@ourdomain.com, and press@ourdomain.com.
The volume of outgoing mail is low – around 100-150 emails a day. These are mostly emails sent by our tech support team from support@ourdomain.com. The other email accounts are not used for email sending and are only monitored from time to time.
As aforementioned, we set the ‘reject’ DMARC policy for the ourdomain.com domain and outsourced the collection of DMARC reports to GlockApps DMARC Analytics.
One day, we received an alert from GlockApps saying
We detected an unusual message count 1376 (+108.00%) for the domain my_company.com on 2021-09-05.
We made the mistake of not paying attention to it at that time. A few days later on, we logged in our dashboard in GlockApps and found this:
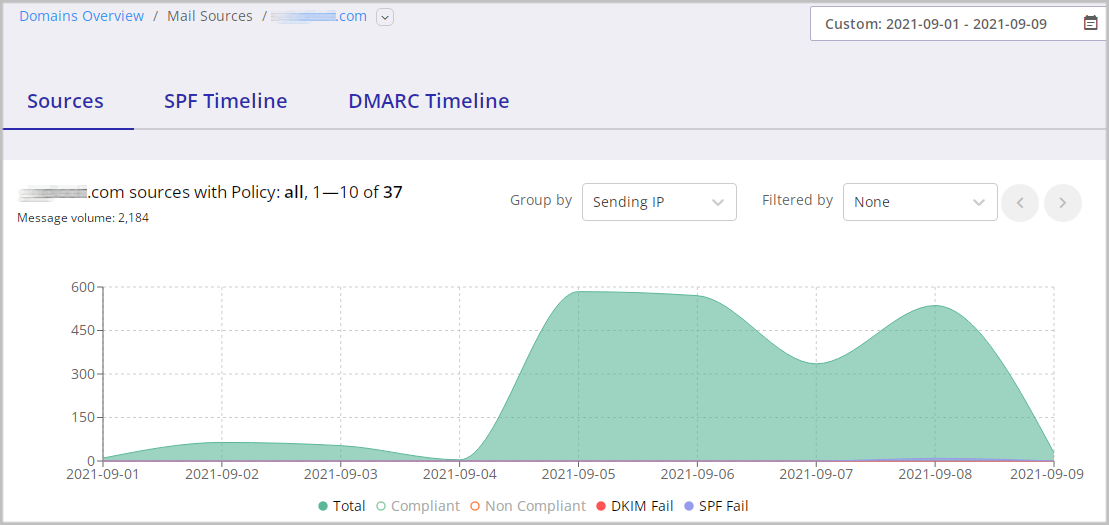
The volume of emails sent from our domain increased a few times over the past days, and it was not a spoofing campaign as the messages were sent from our mail server and from our IP address, and also passed DMARC authentication. So we were confused as to what was going on.
We started the investigation and asked our support team if they had sent any mass mailings in recent days. They said “no.” The admins looked at the logs of our SMTP server and… what a surprise! Spammers hacked one of our mailboxes and started sending spam with links to porno sites. They had sent a few thousand spam messages before we saw the issue. Obviously, it couldn’t stay overlooked by the ISPs.
The consequences were immediate. In Google Postmaster Tools, we saw this:
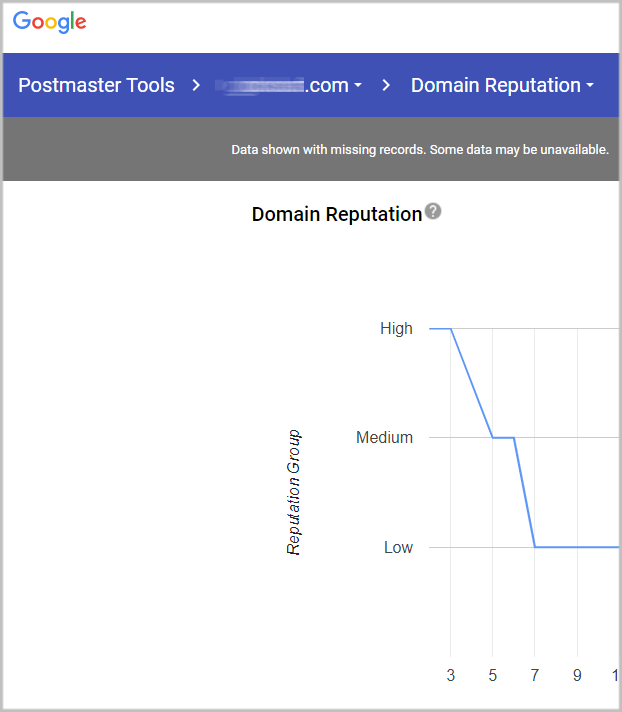
Our domain reputation went from High to Low in just four days.
The most disappointing aspect in all of this was that the GlockApps DMARC alert system detected the problem in time and sent an alert to us, but we didn’t react fast.
What we learned from this case is that even if you set up SPF, DKIM, and DMARC with the ‘reject’ policy, you cannot let it go. You still have to monitor your email traffic and pay attention to any abnormalities. Today, nobody is completely immune to compromised and hacked accounts. If you are a victim of one of these attacks, and the sooner you detect and fix the issue, the lesser the impact.
We want to thank the GlockApps team for a great alert system! It helped us detect a critical issue with one of our accounts and fix it.
Notice from the Glockapps team:
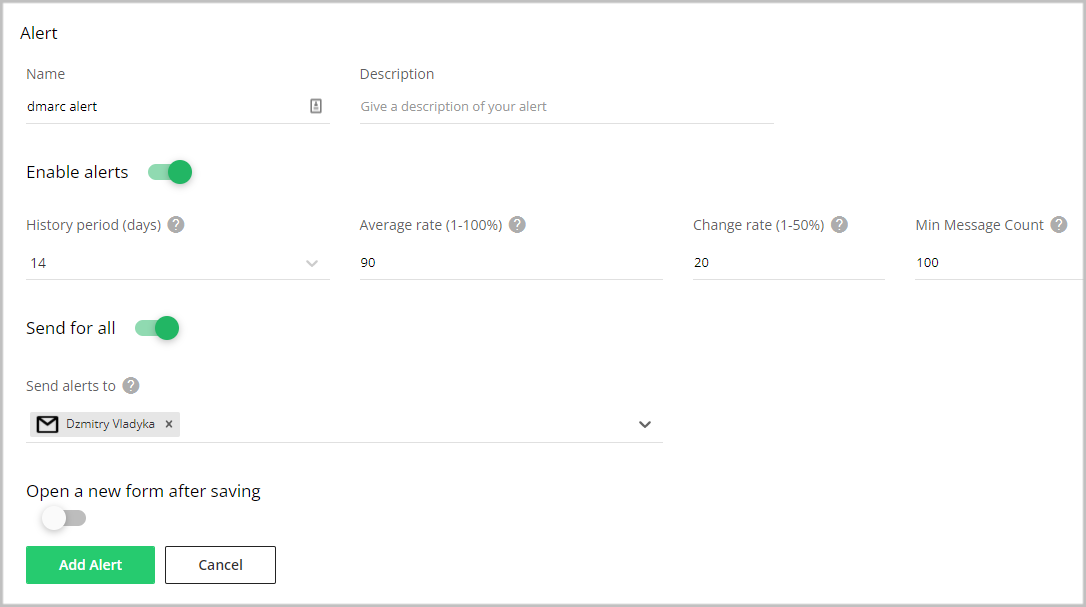
The alert system in DMARC Analytics is not activated by default configuration. To make it work, go to the Alerts menu item after logging into your account at GlockApps and click “Create”. Enter a name for the alert, move the cursor to the active state, select “Send for all” (means the alert will work for all the monitored domains), select where to send the alerts to, and click “Add Alert”. You are done!